Why I Replaced Multipass with OrbStack .
By Noah Makau — DevSecOps Engineer, Entrepreneur, Nerd

Part 1 of 7 — "The Mac Kubernetes Lab: A Production-Mirror Setup from Scratch"
The Problem With My Old Setup
My local Kubernetes setup was embarrassing. At Arkila Systems, I manage EKS clusters with Istio, HashiCorp Vault for secrets, and Crossplane for infrastructure provisioning. My laptop was supposed to reflect some version of that. Instead, I had a pile of Multipass VMs that took a full minute to boot, Docker Desktop fighting for memory in the background, and a list of kubectl port-forward commands I'd memorised because there was no other way to reach anything.
The specific pain points:
Multipass VMs boot in 30–60 seconds and pre-allocate memory whether you use it or not
LoadBalancer services need MetalLB or
port-forwardhacks just to be reachableSwitching between a dev cluster and a production-mirror cluster meant juggling kubeconfigs and hoping nothing crashed overnight
On Apple Silicon, half the tooling had ARM64 quirks that needed a separate debugging session before I could even start the actual work
I spent a weekend trying OrbStack. I didn't go back.
What is OrbStack?
OrbStack is a macOS-native tool that runs Linux virtual machines and Docker containers, built specifically for Apple Silicon. It uses Apple's Virtualization Framework and is written in Swift, Go, Rust, and C — not a port of something designed for x86.
The numbers that made me switch:
| Multipass | OrbStack | |
|---|---|---|
| VM boot time | 30–60 seconds | Under 3 seconds |
| Memory allocation | Pre-allocated at creation | Shared — uses only what's needed |
| Disk per VM | Full image | 1.3–3 GB |
| LoadBalancer services | Needs MetalLB or port-forward | Real IP, works immediately |
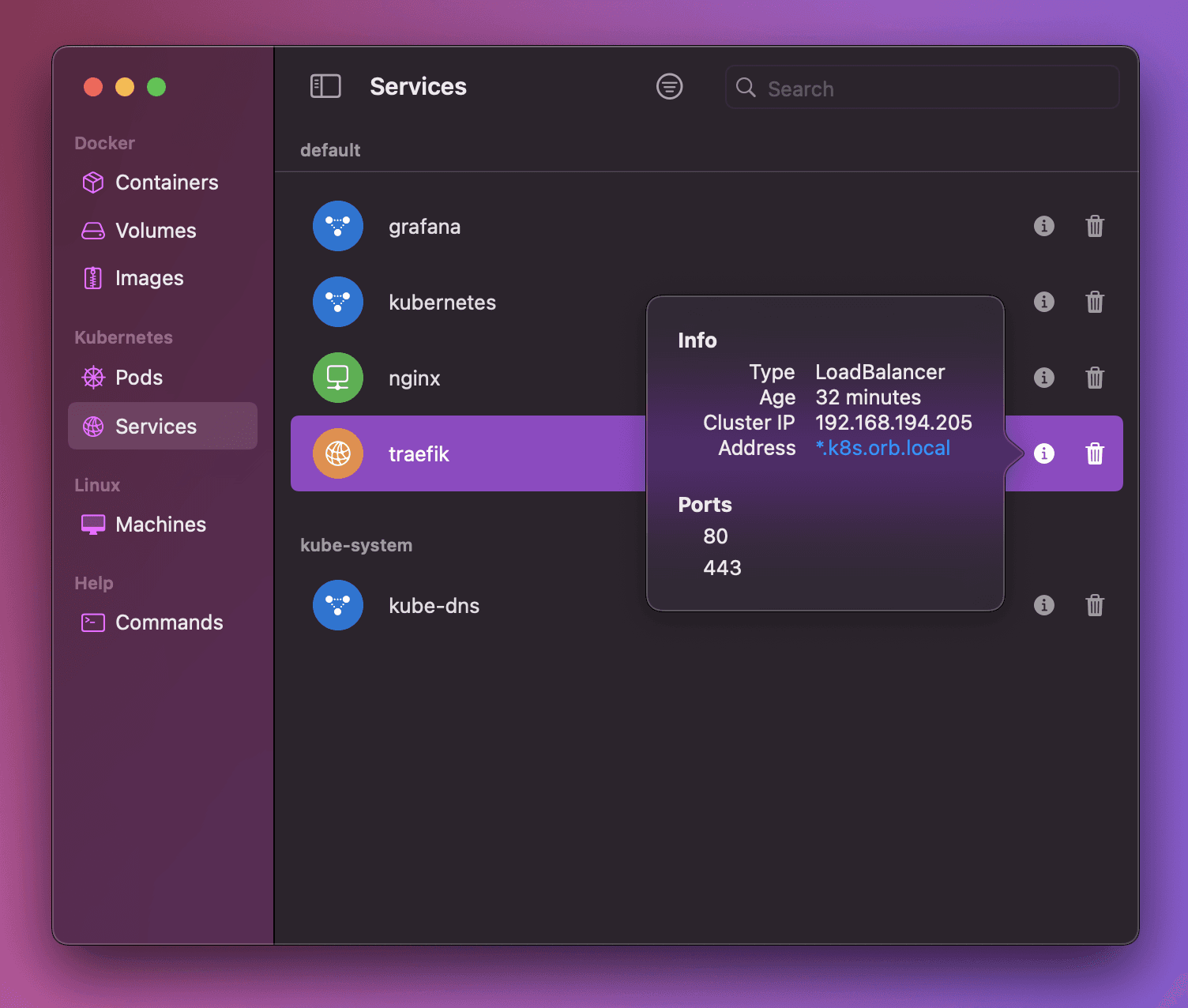
| Wildcard DNS | Manual /etc/hosts | *.k8s.orb.local auto-resolves from Mac |
| Docker Desktop replacement | No | Yes |
OrbStack also ships a built-in Kubernetes cluster — one command and you have a working cluster with real LoadBalancer IPs and wildcard DNS. No configuration required.
💡 Pricing note: OrbStack is free for personal use — which covers everything in this series. If you're planning to roll it out across an engineering team or use it at work commercially, check orbstack.dev/pricing for current plans. The grey area worth knowing: using it on your personal machine for home labs and side projects is free; using it on a work machine to do your day job is commercial use. For this series — personal lab on your own Mac — it costs you nothing.
The Architecture: Two Clusters, One Tool
After a few weeks with OrbStack, I settled on a dual-cluster setup. Two clusters, two purposes.
Image: Dual-cluster architecture — OrbStack native K8s (daily driver) + VM kubeadm cluster (EKS mirror)
Cluster 1 — OrbStack Native K8s (Daily Driver)
The built-in cluster handles fast iteration work:
Crossplane compositions and provider development
HashiCorp Vault AppRole workflows
Helm chart testing
Istio Gateway and VirtualService experimentation — though I break this constantly, which is fine
Switch to it with kubectx orbstack. Services are reachable at *.k8s.orb.local from your browser immediately.
Cluster 2 — VM kubeadm Cluster (EKS Mirror + CKS Lab)
Four OrbStack Linux VMs running a real kubeadm-bootstrapped cluster:
K8s 1.34 — matching our upcoming EKS upgrade target at Arkila Systems
Vault PKI as the cluster Certificate Authority
Istio with revision-based upgrades, identical to our EKS approach
Crossplane with AWS provider
Multi-node topology (control plane + 2 workers) mirroring production
This is also my CKS exam preparation environment — Pod Security Admission, audit policies, NetworkPolicy, short-lived admin certificates via Vault.
Apple Silicon Compatibility — M1 vs M4
I originally built this on an M4 Mac. Everything worked. Then I tried replicating the setup on an M1 Pro. The cluster came up fine, but the CNI never did — and the root cause was not obvious.
| M4 Mac | M1 / M2 / M3 Mac | |
|---|---|---|
| OrbStack VM type | Unprivileged LXC | Unprivileged LXC |
| iptables NAT | ✅ Works | ❌ Restricted |
| Recommended CNI | Calico | Cilium (eBPF) |
| kube-proxy | Standard | Replaced by Cilium |
OrbStack VMs run as unprivileged LXC containers. On M4, iptables NAT table manipulation works fine. On M1 it's restricted — kube-proxy can't write KUBE-SERVICES chains, which means ClusterIP services are unreachable and any CNI plugin that tries to call the API server via ClusterIP fails silently. Calico starts, looks healthy, and then just... doesn't work. Took a while to connect the dots.
The fix is Cilium, which uses eBPF-based service routing and completely replaces kube-proxy. We'll cover this properly in Part 4.
What You'll Need
Apple Silicon Mac (M1, M2, M3, or M4)
Homebrew installed
At least 16 GB RAM — 8 GB will technically work but you'll feel it when all four VMs are running
About 20 GB free disk space
# 💻 Mac — check your chip
system_profiler SPHardwareDataType | grep Chip
# Check available disk
df -h ~
The Multipass → OrbStack Migration
If you're coming from Multipass, the command mapping is straightforward:
| Multipass | OrbStack |
|---|---|
multipass launch ubuntu |
orb create ubuntu |
multipass shell <name> |
ssh <name>@orb |
multipass exec <name> -- cmd |
orb run -m <name> cmd |
multipass list |
orb list |
multipass delete <name> |
orb delete <name> |
multipass stop <name> |
orb stop <name> |
multipass stop --all |
orb stop -a |
Install OrbStack and clean out Multipass:
# 💻 Mac
brew install orbstack
open -a OrbStack # required once for first-time GUI setup
# Remove Multipass
brew uninstall multipass
sudo rm -rf /var/root/Library/Application\ Support/multipassd
sudo rm -rf ~/Library/Application\ Support/multipass
OrbStack auto-installs orb, docker, and kubectl on your PATH.
What's Coming in This Series
Part 1 (this article): Why OrbStack, architecture overview, M1 vs M4
Part 2: Cluster 1 — Native K8s daily driver with Istio, Vault, Crossplane
Part 3: Cluster 2 — VM creation, networking, and Vault PKI bootstrap
Part 4: kubeadm 1.34 — M1 vs M4 CNI deep dive (Calico vs Cilium)
Part 5: Istio revision-based upgrades and MetalLB on the VM cluster
Part 6: Vault K8s auth and Crossplane — mirroring your EKS stack
Part 7: Day 2 operations, CKS lab scenarios, and making it all stick
Part 2: Cluster 1 — Your Daily K8s Driver in One Command →
Noah Makau is a DevSecOps Engineer, Entrepreneur, and self-described Nerd. He holds CKA, CKAD, AWS Solutions Architect Professional, AWS Solutions Architect Associate, and AWS Cloud Practitioner certifications. He is the founder of Arkila Systems, a DevOps consultancy — where he designs and operates Kubernetes, HashiCorp Vault, Crossplane, and CI/CD pipelines at scale. He is currently preparing for CKS certification.